The Week the Toolchain Became the Kill Chain
Cisco SD-WAN, a supply chain worm, and an AI agent that let anyone in. They weren't three separate stories.
There's a version of threat intelligence coverage that treats each incident as its own discrete event. Breach here, CVE there, ransom demand somewhere else. Triage them, patch them, move on. I've read enough of those roundups to know they're useful and kind of exhausting at the same time.
This week wasn't like that. Three things happened in roughly five days that felt less like independent incidents and more like the same argument being made from different angles. Cisco SD-WAN under active exploitation by a persistent, sophisticated threat actor. A supply chain worm that defeated cryptographic provenance controls and compromised 172 packages across npm and PyPI, including Mistral AI SDK packages and the @tanstack namespace. And a multi-agent AI framework that shipped with authentication hard-coded to disabled and got scanned within four hours of its CVE going public.
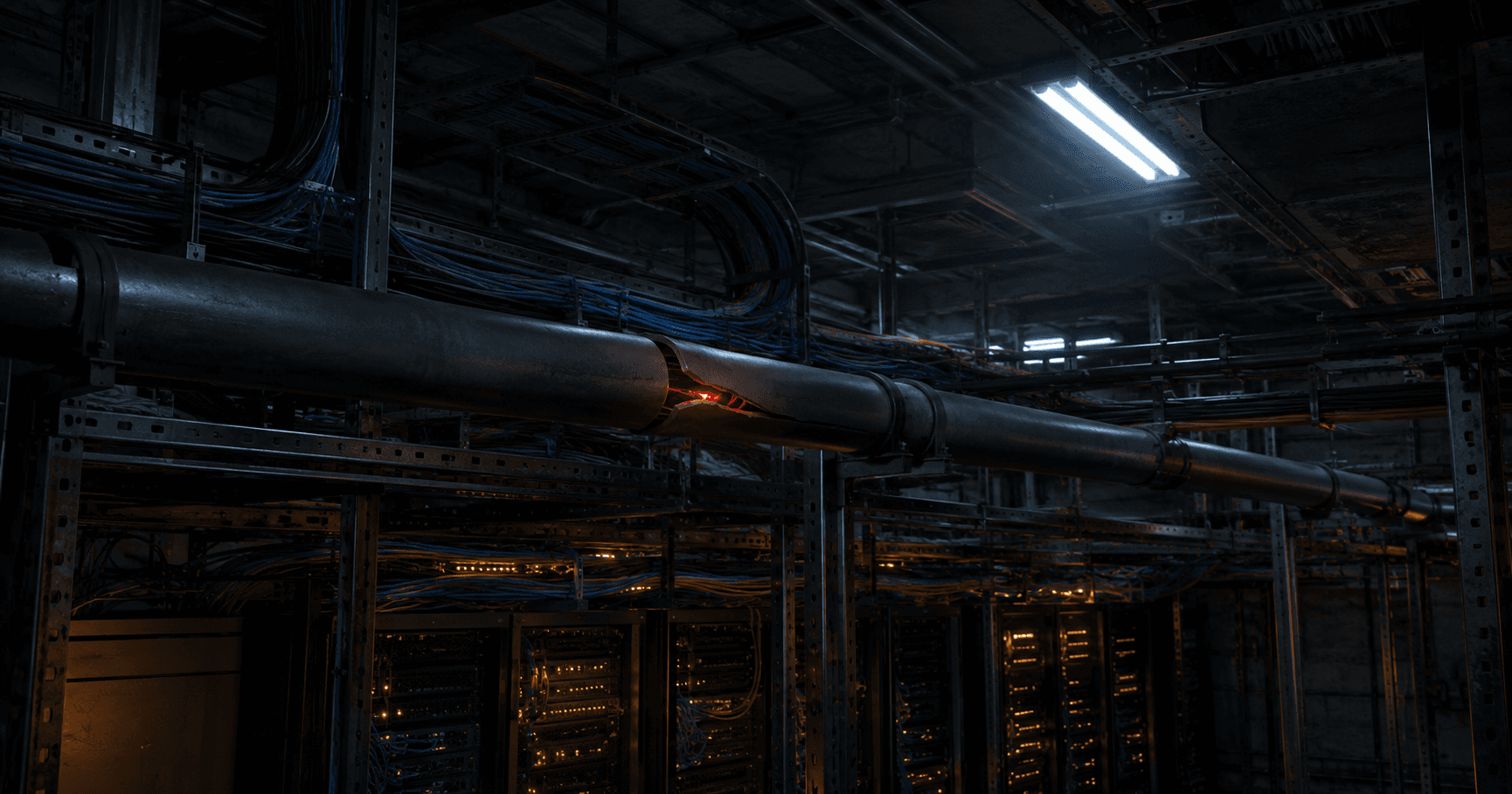
None of these are endpoint attacks. None of them required phishing an employee or brute-forcing a login. What they share is that they all hit the layer your organization implicitly trusts: the network control fabric, the software supply chain, the AI orchestration platform. The plumbing, basically. And nobody was watching the plumbing.
The SD-WAN Control Plane Is Not a Backwater
Let me start with the Cisco story, because I think it's the one most likely to get quietly deprioritized by teams who see "CISA KEV addition" and drop it into the patch queue for next Tuesday.
Don't do that.
CVE-2026-20182 is a CVSS 10.0 authentication bypass in Cisco Catalyst SD-WAN Controller and Manager. The flaw lives in the control connection handshake, the process by which SD-WAN devices establish trust with each other. An unauthenticated remote attacker sends crafted requests that exploit a validation failure in that handshake and walks out the other side as an authenticated peer with administrative privileges. No credentials needed. No social engineering required. Just a broken assumption about how trust gets established at the protocol level.
CISA added it to the KEV catalog on May 14, reinforcing Emergency Directive 26-03 -- a directive CISA originally issued in February in response to active exploitation targeting Cisco SD-WAN systems -- and giving federal civilian agencies until May 17 to remediate. That's a 72-hour window. CISA reserves Emergency Directives for situations where the standard KEV remediation process isn't moving fast enough -- issuing one signals the agency assessed active exploitation as an immediate operational risk, not a scheduled patch item. When CISA reaches for that mechanism, the message is not subtle.
What makes this more than a patching story is who's been exploiting it and for how long. Cisco Talos attributes active exploitation to a threat actor designated UAT-8616, a sophisticated cluster that's been targeting Cisco SD-WAN infrastructure since at least 2023. This isnt opportunistic scanning by a script kid who found a PoC on GitHub. UAT-8616 used CVE-2026-20182 alongside four other SD-WAN CVEs as part of a coordinated campaign, and their post-compromise playbook is methodical: SSH key injection, NETCONF configuration manipulation across the entire SD-WAN fabric, malicious account creation, extensive log clearing. They also leveraged a software version downgrade technique to chain an older vulnerability for root escalation. Their infrastructure overlaps with Operational Relay Box networks, which is how serious actors build resilient, hard-to-attribute command and control.
Here's the thing about SD-WAN that I keep coming back to: when you compromise an SD-WAN controller, you're not compromising a single device. You're compromising policy distribution across the entire fabric. You don't own a box, you own the blueprint. Everything downstream is yours to reconfigure.
There are multiple CVEs tied to this campaign. CISA has confirmed at least CVE-2026-20127, CVE-2026-20133, and CVE-2026-20182 in its KEV catalog, with additional vulnerabilities referenced throughout ED 26-03 guidance. If your organization runs Cisco Catalyst SD-WAN and hasn't gone through the hunt and hardening guidance CISA published alongside that directive, that's the starting point right now.
The Supply Chain Ate Itself
The Mini Shai-Hulud story is the one I couldn't stop digging into this week, and the more I read the worse it got.
On May 11, threat actor TeamPCP launched a coordinated attack across npm and PyPI. Over 48 hours they compromised 172 unique packages across 403 malicious versions, including the entire @tanstack namespace, Mistral AI's official TypeScript and Python SDKs, UiPath's automation tooling, OpenSearch, and Guardrails AI -- figures reported across multiple security researchers and advisories. @tanstack/react-router alone had over 12 million weekly downloads at the time of the attack. The affected packages collectively represent more than 518 million cumulative downloads.
But the scale isn't even the most important part. The technique is.
TeamPCP didn't steal credentials to push malicious packages. They hijacked TanStack's legitimate release pipeline and used its own trusted identity to publish. The attack chained three separate weaknesses: a pull_request_target "Pwn Request" misconfiguration that let fork-controlled code run in a privileged workflow context, GitHub Actions cache poisoning across the fork and base trust boundary, and runtime memory extraction of an OIDC token from the Actions runner process. When TanStack's legitimate release workflow ran, it restored a poisoned cache. The injected code read the runner's process memory to extract the ambient OIDC token, and 84 malicious package versions were published in two batches, six minutes apart, using the legitimate GitHub Actions publisher identity.
The published packages carried valid SLSA provenance, a cryptographic certificate generated by Sigstore that's specifically designed to verify a package was built from a trusted source. The packages had the right signatures, from the right identity, through the right pipeline, because the pipeline itself was compromised. The trust signal you were relying on was accurate, the thing behind the signal was not.
The PyPI side of the campaign used a different delivery mechanism. The mistralai 2.4.6 payload appended a 13-line backdoor to __init__.py that fired on import, downloading a second-stage payload from a hardcoded IP using curl with TLS verification disabled. PyPI quarantined the entire mistralai project. Any environment that imported mistralai during the attack window should be treated as potentially compromised regardless of how the install ran, because the payload fires on import, not on install.
If this pattern feels familiar, it should. When I wrote about the Instructure Canvas breach a few weeks back, the central problem was a trusted SaaS platform becoming the pivot point into thousands of downstream institutions. Mini Shai-Hulud is the same structural failure one layer deeper: it's not the application being compromised, it's the tooling that builds the application. TeamPCP is specifically targeting the places developers trust without thinking about it, because those are the places that aren't governed.
For anyone whose environments ran affected packages on May 11 or 12: rotate everything. npm tokens, GitHub tokens, cloud credentials across AWS, GCP, and Azure, Kubernetes service account tokens, HashiCorp Vault tokens, and deployment secrets. Don't stop at npm tokens. If the runner touched it, treat it as burned. The malware specifically targeted password vaults including 1Password and Bitwarden, which is an escalation from previous TeamPCP waves.
The Agentic AI Attack Surface Is Here and Nobody's Ready for It
The PraisonAI story is smaller in scale and more important in what it signals.
PraisonAI is an open-source multi-agent orchestration framework with roughly 7,000 GitHub stars at the time of reporting. Not a major enterprise platform, not a household name. CVE-2026-44338 is a missing authentication flaw in a legacy Flask API server that ships with AUTH_ENABLED = False and AUTH_TOKEN = None hard-coded into the codebase. The authentication check returns True whenever authentication is disabled, so two "protected" routes fail completely open: GET /agents returns all configured agent metadata, and POST /chat executes the entire configured workflow for any caller who sends a JSON body with a message key. The submitted message value is ignored. Whatever your agents.yaml is configured to do, any unauthenticated caller can trigger it.
That's an embarrassing default for any software in 2026, let alone an agentic AI framework. But the disclosure story is what actually matters here.
Sysdig's threat research team observed a scanner, identifying itself as CVE-Detector/1.0, probing the exact vulnerable endpoint on internet-exposed instances within three hours and 44 minutes of the advisory going public. On a project with roughly 7,000 stars. The scanner didn't need to understand what the agent did or what permissions it had. It just needed the authentication check to fail open, and then it moved on to the next target.
The implications are uncomfortable. Any AI agent deployment you have running, whether its PraisonAI or something else, that has an authentication default you haven't explicitly verified, that binds to 0.0.0.0 rather than localhost, that nobody has assessed for what an unauthenticated workflow trigger actually does in your environment: that's exposure waiting to be found. The blast radius isn't arbitrary code execution in the traditional sense. The blast radius is whatever permissions you gave the agent. In production that typically means LLM provider access, code interpreters, shell execution, file I/O, and API integrations with everything the agent was deployed to touch.
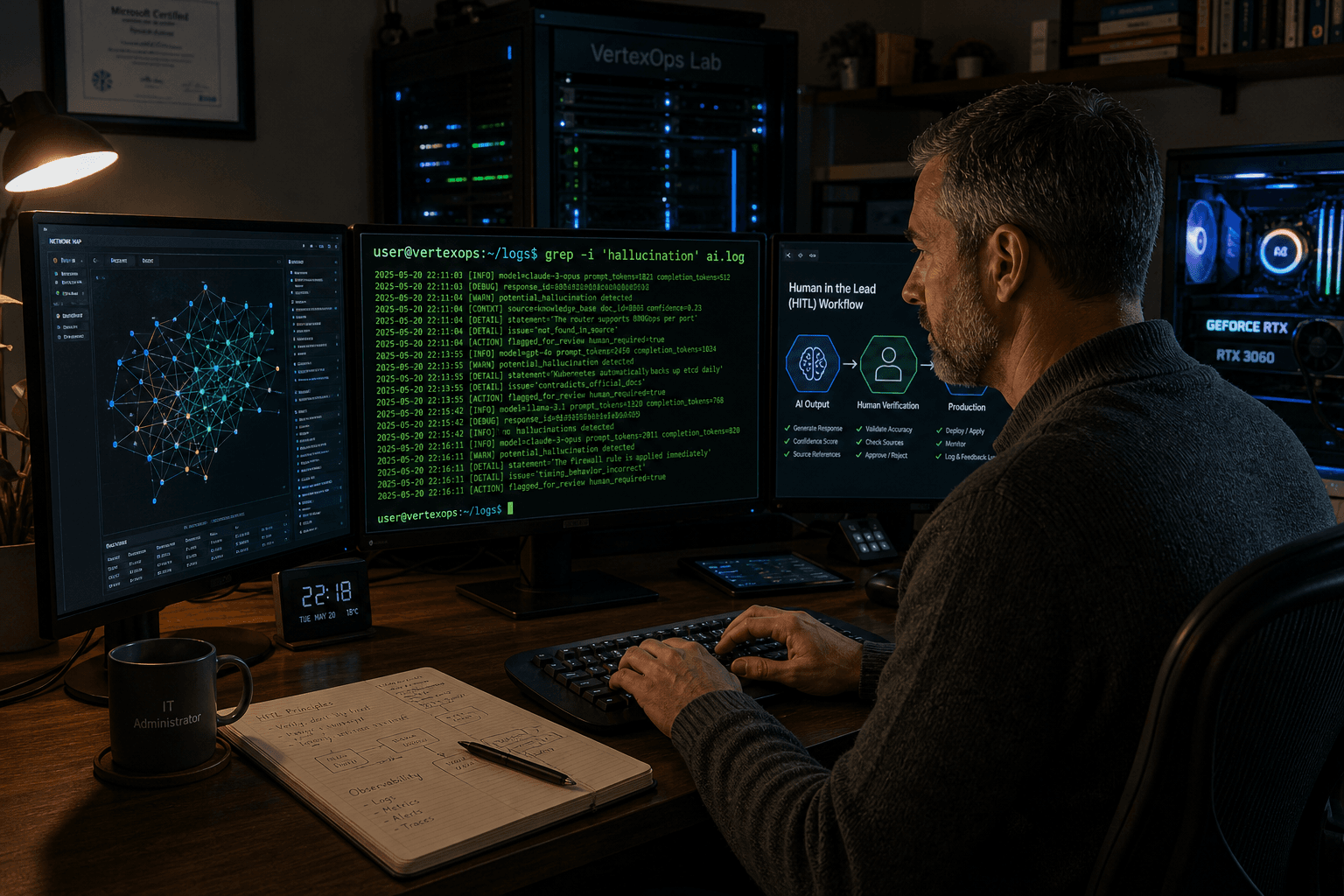
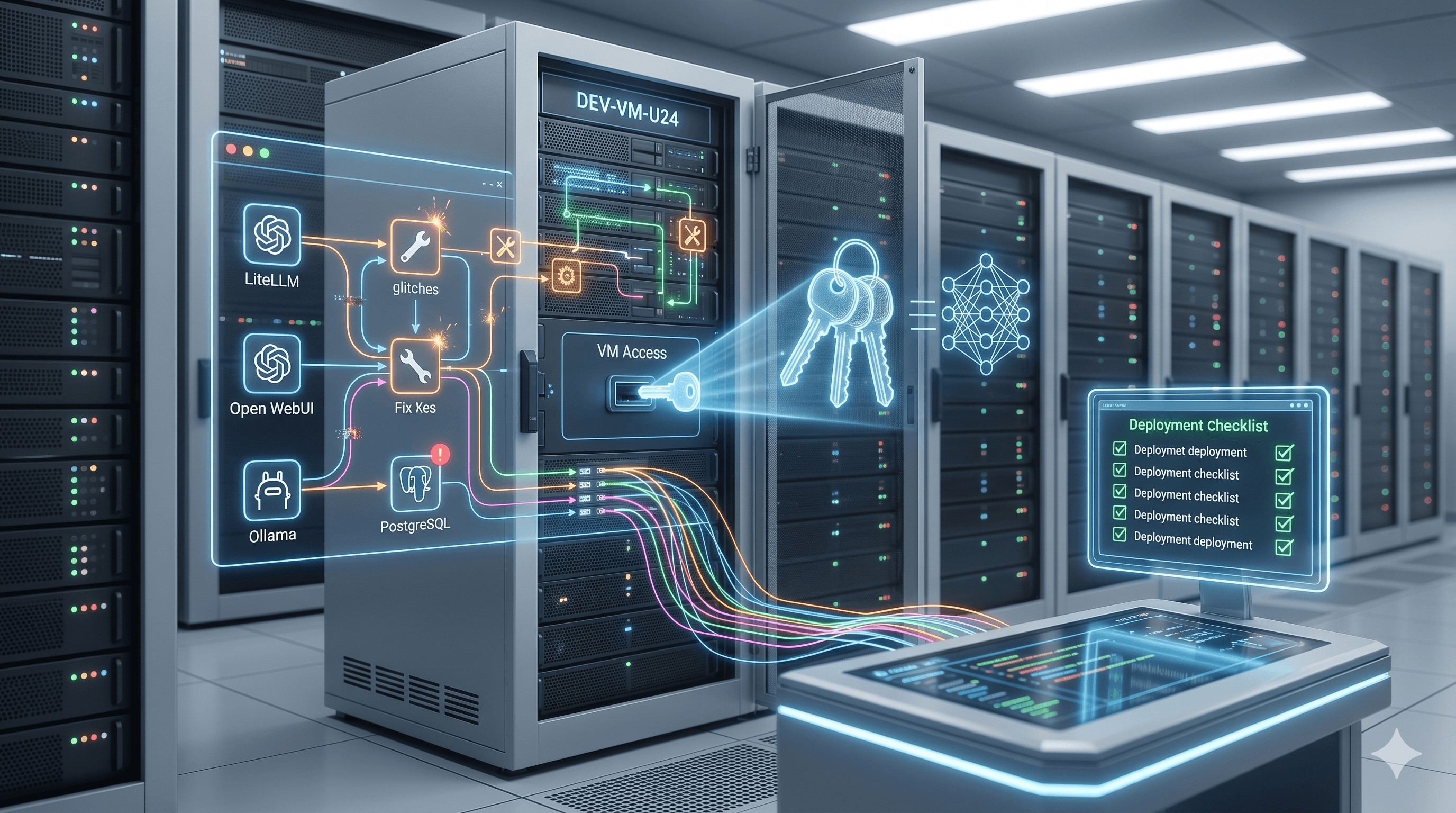
I've written before about handing Claude Code the keys to a fresh VM and watching what breaks. What's been become clear watching this week unfold is that the security community hasn't caught up to where AI deployment already is. Agentic frameworks are in production, executing tasks, consuming credentials, and taking actions, most often without meaningful security oversight or even a basic inventory. CVE-2026-44338 is small on its own. As evidence that adversary tooling is already scanning specifically for exposed AI agent surfaces, and doing so in single-digit hours after disclosure, it's a data point that should change how you think about your agentic AI posture.
The Pattern
None of this week's incidents required compromising an endpoint. UAT-8616 didn't need a foothold on a developer's laptop to reconfigure the SD-WAN fabric. TeamPCP didn't need to phish a TanStack maintainer, they went around them through the pipeline. The PraisonAI scanner didn't need to understand the agent's configuration, it just needed the auth check to fail.
What connects them is that each attack targeted a layer of infrastructure that organizations trust deeply and govern badly. The network control plane. The software supply chain. The AI orchestration layer. These are the systems that run everything else. When defenders are focused on endpoint telemetry and perimeter controls, these surfaces are already exposed and increasingly well understood by the people who want to use them.
TeamPCP has been developing this worm infrastructure across multiple campaign waves since late 2025. UAT-8616 has been working Cisco SD-WAN vulnerabilities since at least 2023. The PraisonAI scanner found a fresh CVE in under four hours because it was already running, already looking, already optimized for the AI agent surface specifically.
None of this is new in the sense of being unprecedented. What's new is the speed, the tooling, the scale, and the fact that the AI layer is now firmly in scope. The toolchain is the kill chain. If your organization isn't governing it with the same rigor you apply to production systems -- and in a lot of organizations, that's a significant if -- this week is a reasonable illustration of what that gap looks like when someone decides to use it.