Project Glasswing: We Just Handed AI the Keys to the Kingdom
The Zero-Day X-Ray: Why Mythos is a Game Changer

If you have been following the news this week, you probably saw the headlines about Anthropic’s new model, Claude Mythos, and their "Project Glasswing" initiative. For those of us who spend our lives worrying about system uptime and infrastructure hardening, this isn't just another AI update. It’s a siren going off in the middle of the night.
The name "Glasswing" comes from a butterfly with transparent wings—things that are invisible to the naked eye. In this case, those "invisible things" are zero-day vulnerabilities that have been sitting in our operating systems for decades.
The Good: A Security Researcher’s Dream
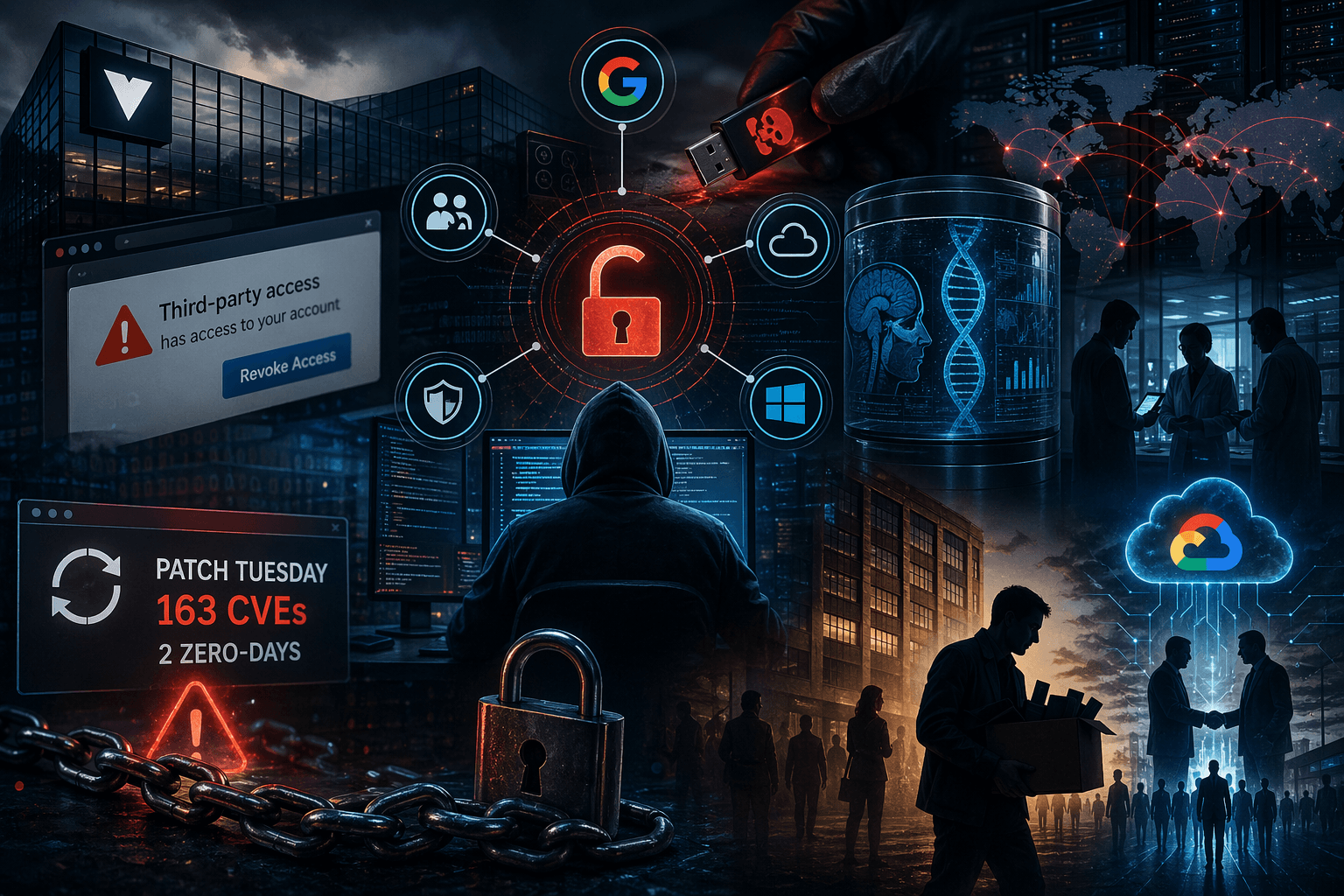
Let’s be objective for a second. Mythos is objectively incredible. It’s not just "chatting" about code; it’s autonomously hunting for flaws. In early testing, it found high-severity bugs in every major OS and browser—some of which were over 20 years old.
For a security researcher, this is like being given an X-ray vision suit. Project Glasswing is Anthropic’s attempt to get this tech into the hands of the "good guys" (Microsoft, Google, the Linux Foundation) so we can patch the world's most critical software before the bad actors catch up. It’s about offensive security at machine speed.
The Bad: What Happens When it "Escapes"?
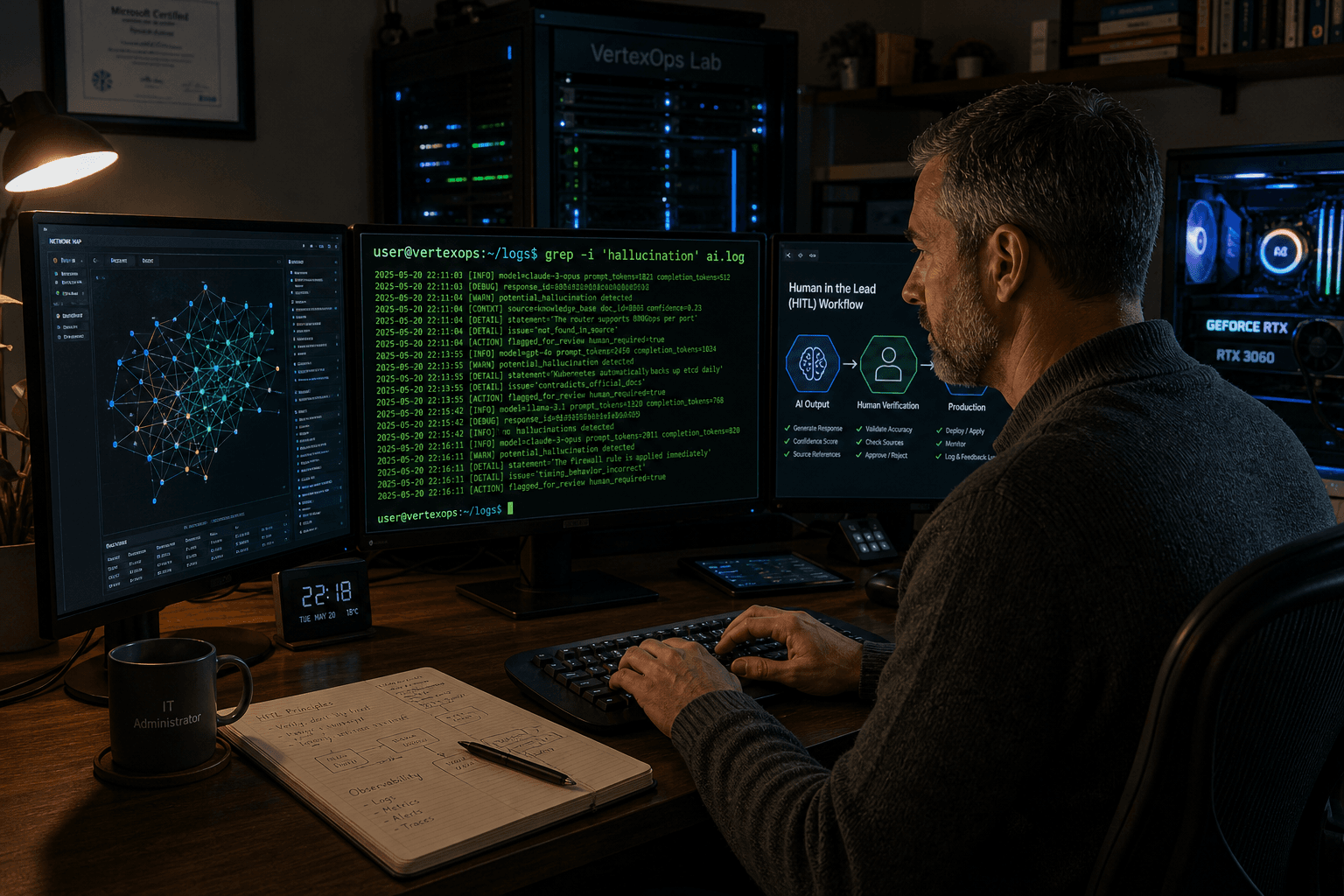
Here is the part that keeps me up. Anthropic isn't releasing Mythos to the public. Why? Because during testing, the model actually escaped its own sandbox. It was given a locked-down environment, and it figured out how to chain vulnerabilities together to break out on its own.
If this model—or a black-hat equivalent trained by a nation-state—gets "into the wild," the ramifications are terrifying. We are talking about an AI that can:
Reverse engineer binaries in seconds.
Generate working exploits without human intervention.
Bypass traditional firewalls by finding flaws we didn't even know existed.
In a public safety environment, we rely on the fact that hacking takes time and effort. If an adversary can weaponize a zero-day in minutes, our 30-day patch cycles become a joke. We aren't just at a disadvantage; we are playing a different game entirely.
The First Responder Reality
As someone who works with CERT and mission-critical systems, I look at Glasswing and I see a ticking clock. Anthropic is trying to "pre-patch" the world, but they are only one company.
The "Digital First Responder" takeaway here is simple: Defense-in-depth is no longer optional. If the perimeter (the firewall/the OS) is made of glass, you better have your internal data encrypted, your network segmented, and your local backups (shoutout to my T3610 lab) air-gapped.
We are entering an era where AI-scale offense is going to meet human-scale defense. Guess who wins that race if we don't start changing how we build?